An Android flaw found on MediaTek phones could cause your PIN to be bypassed in less than a minute
Once exploited, attackers can recover your phone’s PIN, unlock encrypted storage, and even extract sensitive data such as cryptocurrency wallet phrases. Security researchers estimate that approximately one in four Android phones could be affected, especially budget phones.
Sign up for my free CyberGuy report Get the best tech tips, breaking security alerts, and exclusive deals delivered straight to your inbox. For simple, realistic ways to spot scams early and stay protected, Visit CyberGuy.com – Trusted by millions who watch CyberGuy on TV daily. In addition, you will get instant access to my The ultimate scam survival guide Free when you join.
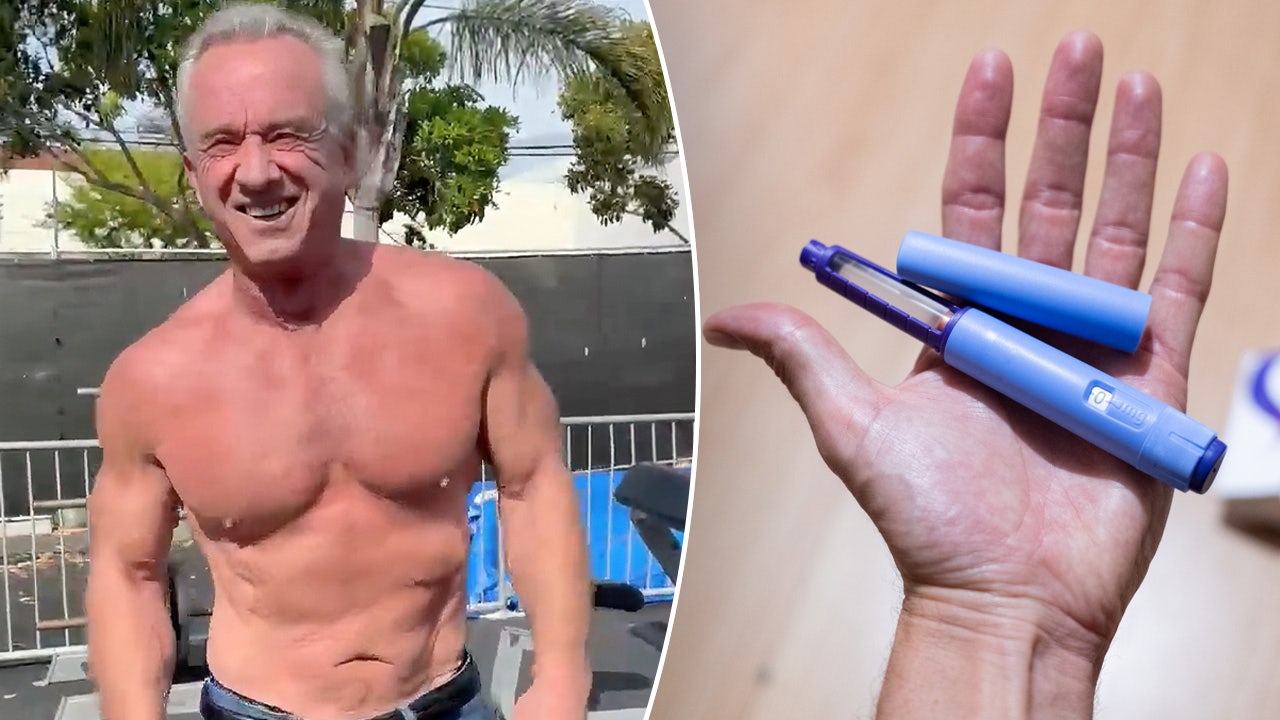
Android fixes 129 security vulnerabilities in the phone’s major update

The March Android security update fixes 129 vulnerabilities, including a zero-day vulnerability that has already been exploited in targeted attacks. (Firdaus Nazir/Noor Photo)
All about Android hacking vulnerability
The newly disclosed vulnerability, tracked as CVE-2026-20435 in the National Vulnerability Database, affects some Android phones backed by MediaTek, a major smartphone chip maker based in Taiwan that competes with companies like Qualcomm. These phones use a security component called Trustonic’s Trusted Execution Environment (TEE), which is designed to keep sensitive data, such as encryption keys, protected from the rest of the system.
It stores encryption keys that help keep your device encrypted and secure, even if someone tries to tamper with it. However, security analyzes of the vulnerability indicate that these protections may be bypassed on affected devices.
By connecting the phone to the computer using a USB cable, an attacker with physical access may be able to exploit the flaw during the early boot process, potentially exposing sensitive data before full security protection is enforced. Think of it like reaching for the master key before the safe door closes. Once attackers gain access to these low-level components, they may be able to access encrypted storage without needing your PIN.
In a worst-case scenario, this type of access could allow attackers to extract highly sensitive information, including personal photos, stored passwords, private messages, financial data, and crypto wallet credentials. If crypto wallet seed phrases are exposed, attackers can permanently drain funds.
What are Android makers doing about it?
There are limited actions that manufacturers can take on their own since the issue originates at the processor level, which is manufactured by MediaTek. The company says it has released a firmware patch to address the vulnerability. However, the update still needs to be distributed by individual phone manufacturers through security updates. Depending on the device and whether it is still supported, this update may arrive quickly or not at all.
The good thing is that this attack requires physical access to the phone and a USB connection to the computer. This means that it cannot be done remotely over the Internet. However, if your phone is stolen, briefly confiscated, or even taken during repair, it’s possible that an attacker could extract sensitive information.
If you’re not sure if this vulnerability affects your mobile device, you can look up your phone on a platform like GSMArena or the vendor’s website to see which SoC it uses, then check it using MediaTek’s March security bulletin under CVE-2026-20435. You can log in corp.mediatek.com/product-security-bulletin/March-2026 To review the list of affected chipsets and check if your device is at risk.
CyberGuy reached out to MediaTek for comment, but did not receive a response before the specified deadline.
A new Android attack tricks you into giving you dangerous permissions

A new Android banking Trojan called Sturnus can take over your screen, steal your banking credentials, and even read encrypted chats from apps you trust. (Delmen Dunson/Getty Images)
How to know if your phone is affected or not
So how do you know if your phone is really at risk? Not every Android phone is at risk. The issue mainly affects devices using certain MediaTek processors. Here’s how to check your phone:
1) Find your phone model
Go to Settings > About phone And search for your exact model name.
2) Find the processor (chip)
Look into your Phone model On a site like GSMArena or the manufacturer’s website to find the processor (also called SoC).
3) Check if it uses MediaTek
If your phone is used MediaTek chipmay be affected. Devices with Qualcomm Snapdragon or Google Tensor chipsets are not part of this specific issue.
4) Install the latest security updates immediately
Check your phone’s system update settings and install any updates available from the manufacturer. Go to Settings > Software update And install any Updates available. MediaTek has already released a fix, but phone makers will have to distribute it. Installing updates quickly ensures that you get a firmware patch if your device manufacturer releases it.
7 ways you can protect your phone from hacking
If your phone uses one of the affected SIM cards, some simple precautions can help reduce the chances of someone accessing your data if the device falls into the wrong hands.
1) Install strong antivirus protection
The security application cannot fix this flaw at the processor level. However, it can still help protect your phone from other threats that often follow stolen or compromised devices. This won’t stop the specific exploit, but it can detect malicious apps, spyware, and suspicious activity that attackers may install after gaining access. This extra layer of monitoring can help prevent additional data theft if your device falls into the wrong hands. Get my picks for the best antivirus protection winners of 2026 for Windows, Mac, Android, and iOS at Cyberguy.com
2) Avoid keeping sensitive information on your phone
If you store things like cryptocurrency wallet seed phrases, recovery codes, or… Sensitive documents For notes or screenshots apps, consider moving them to a secure, offline location. If someone extracts your phone data through this vulnerability, this information could be exposed.
3) Maintain physical control of your phone
This exploit requires someone to physically connect your phone to your computer. Don’t leave your device unattended in public places, and be careful when handing it over to unknown repair shops or technicians. Physical access greatly increases the risk.
4) Use strong screen locks and auto-lock settings
While the vulnerability bypasses encryption on affected devices, Strong lock settings It still protects against many other threats. Use a longer PIN or passcode instead of simple patterns, and enable automatic locking after short periods of inactivity.
5) Protect accounts with two-factor authentication
Even if attackers gain access to data on your phone, two-factor authentication (2FA) can prevent them from logging into your online accounts. Enable it for email, banking apps, cloud storage, and social media where possible.
6) Use a password manager
A password manager stores your login credentials in a secure, encrypted vault instead of leaving them scattered across apps and notes. If someone hacks your device, your password manager will still protect your accounts with strong encryption, forcing attackers to breach another layer of security before they can access your logins. Check out the best expert-reviewed password managers of 2026 at Cyberguy.com
7) Enable USB Restricted Mode (if available)
Some Android devices limit access to USB data when locked. Turning this setting on can reduce the risk of unauthorized data extraction over a wired connection, especially in situations where someone has physical access to your phone for a brief period. on Samsung phones Run the latest software:
Settings may vary slightly depending on Samsung model and software version.
Go to Settings
handle Screen lock
Then press Secure lock settings
He enters Your current PIN, Then press He continues
maybe “Network lock and security” (or a similar named option) to help block access to USB data while your device is locked.

ZeroDayRAT spyware can secretly access messages, camera feeds and banking apps on infected iPhone and Android devices. (Stefan Sauer/Image Alliance)
Key takeaway for Kurt
This vulnerability exposes a deeper problem in the Android ecosystem. Even when chip manufacturers release a fix, millions of phones rely on manufacturers to deliver updates that may never arrive, especially for cheaper devices that quickly lose support. We often assume that our lock screen and encryption will protect our data if the phone is lost or stolen. However, such incidents show that protectionism is only as strong as the modernization policies behind it. When devices stop receiving security patches, those protections weaken over time.
Should phone manufacturers be required to guarantee security updates for several years if their devices contain serious security vulnerabilities? Let us know by writing to us at Cyberguy.com
Click here to download the FOX NEWS app
Sign up for my free CyberGuy report Get the best tech tips, breaking security alerts, and exclusive deals delivered straight to your inbox. For simple, realistic ways to spot scams early and stay protected, Visit CyberGuy.com – Trusted by millions who watch CyberGuy on TV daily. In addition, you will get instant access to my The ultimate scam survival guide Free when you join.
Copyright 2026 CyberGuy.com. All rights reserved.












Post Comment